It also reveals that investigators are increasingly focusing on attackers using Microsoft products to hide in sight.
Cybersecurity experts and US officials said weeks ago that the attackers may have misused credentials and impersonated legitimate users for the spying campaign.
Now the Department of National Security’s Cybersecurity and Infrastructure Security Agency has confirmed this, describing step-by-step how the attackers concealed their tracks.
First, the attackers gained initial access to the victim by taking advantage of a previously disclosed SolarWinds vulnerability or through other methods, such as guessing the password, which CISA said it was still investigating.
Next, the attackers sought to impersonate one or more real users in order to gain access to the enterprise’s cloud services and identity management provider, such as Microsoft 365 or Azure Active Directory.
Security experts have described services such as Azure Active Directory as carrying “the keys of the kingdom” because for many organizations, it is the software used to create and manage network accounts, passwords, and privileges.
Once the attackers gained access to the organization’s identity provider, CISA said, they were able to set up permissions for themselves to surreptitiously access other programs and applications.
Robert M. Lee, CEO of cybersecurity firm Dragos, said attacks on a platform like Active Directory can be extremely powerful.
“It is a system that connects all the other systems,” he said in a recent interview.
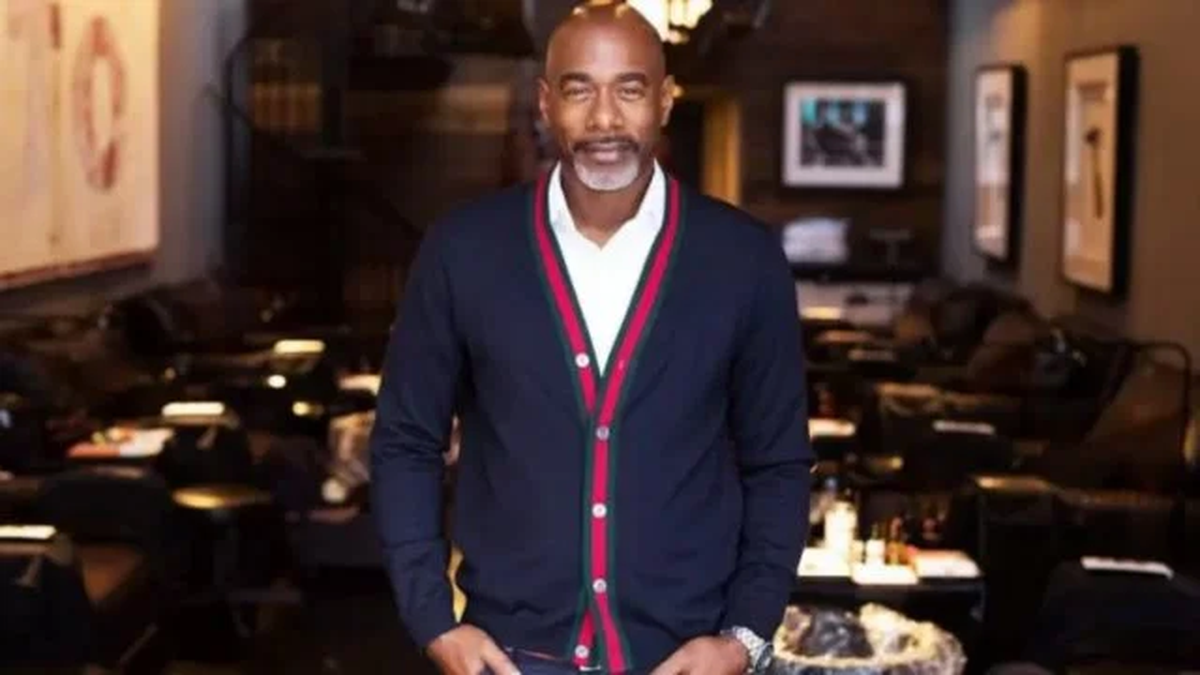
Cedric Layton, a former National Security Agency official and military analyst, told CNN that the report showed the sophistication of the attackers.
“This is the latest key to understanding the SolarWinds hack,” Leighton said. “The fact that the credentials were compromised – including multi-factor identity authentication systems – shows how widespread this attack actually is. References to lateral traffic show that they moved across networks to compromise more data than was originally thought. Basically, this is recognition that compromise is The potential for our systems goes far beyond what was originally reported. This is a very big problem. “
Zachary Cohen contributed to this story.